Events
IS&T Seminar Series – Digital Transformation in the Enterprise

- Wednesday, April 24th 2019
- Eric Barnes
- Wawa
The way people are interacting with technology is changing from system centric to people enablement. Learn how the traditional enterprise model needs to change in order to keep up with today’s end-user population. Understand how companies have empowered their employees by bringing technology closer to the business and what cultural changes are needed to take advantage of today’s technology landscape. How can companies move from monolithic development and design to agile and design thinking? What does it mean to be have a “Hybrid” infrastructure and how does this benefit or hurt a business? What about security in the Digital Age? This discussion will focus on these key aspects and more as we examine what it takes to move the enterprise into the digital age.
IS&T Seminar Series – WCU Cabinet: Dr. R. Lorraine (Laurie) Bernotsky

- Monday, March 4th 2019
- Dr. Laurie Bernotsky
- West Chester University
Dr. Laurie Bernotsky is West Chester University’s Provost and Executive Vice President. As Provost, she is the Chief Academic Officer overseeing WCU’s Deans and Faculty and providing leadership for the University’s Teaching and Learning Mission. As EVP, she is the Chief Operating Officer providing oversight for the business operations of the University and serving as the senior-most advisor to the President. Please join us on Monday March 4th for a presentation and discussion with Dr. Bernotsky and a unique opportunity to learn about these two distinct leadership roles and how she balances them.
IS&T Seminar Series – Digital Disruption and the Future of IT

- Wednesday, November 28th 2018
- Thomas DeChiaro
- Drexel University
Higher Education in the United States is being forced to confront changing economics, demographics, and competitive landscapes. The colleges and universities that prosper during challenging times are learning to embrace digital capabilities to teach, learn, and do business in new ways.
IS&T Seminar Series – Wharton Interactive: Revolutionizing Games Based Learning

- Wednesday, November 7th 2018
- Sarah E. Toms
- University of Pennsylvania
Education practices have failed to keep pace with what the research has been telling us for decades about the efficacy of integrating interactive modes into learning.
Wharton Interactive is on a mission to transform education by closing the gap between instructional research and the outdated educational practices. Sarah Toms, co-founder and executive director will share the future she and her award winning team at The Wharton School are building—namely innovative solutions, gaming platforms, and best practice frameworks that accelerate educator's abilities to modernize curricula and integrate novel experiences that serve to make learning more meaningful, and knowledge more applicable.
IS&T Seminar Series – TechSavvy Manager: Leveraging IT to Achieve Strategic Advantage

- Thursday, June 21st 2018
- Dr. Sassan Hejazi
- Kreischer Miller
When it comes to IT issues, there seems to be a significant gap between IT and non-IT managers in regards to priorities and efforts. This presentation is intended to bridge the gap between the parties and develop a common framework of understanding between IT and not-IT management, focused on enabling the organization to harness the power of IT for a competitive advantage.
IS&T Seminar Series – Active Learning at Penn – Moving from Experiment to Commitment

- Wednesday, May 30th 2018
- John MacDermott & Jeff Douthett
- University of Pennsylvania
Active Learning Classrooms and Pedagogy at Penn started small, but have grown rapidly. Join John & Jeff as they discuss how they got started, current initiatives and future directions. They’ll look at some of the challenges of making the transition from a relatively small experiment to a University-level commitment in Penn’s decentralized environment. Their Classrooms Committee, Center for Teaching & Learning, Libraries, Registrar’s Office, IT groups and others are all involved. They are collaborating to develop the facilities, pedagogical practices & support systems needed for scalable & sustainable changes in teaching & learning.
IS&T Seminar Series – “IT Takes a Village” on Info Security

- Wednesday, May 9th 2018
- Pablo Molina
- Drexel University
Facebook, Equifax, the Office of Personnel Management, fake news, ransomware… a faulty moral compass for technology decisions costs organizations much money and reputation. Join Dr. Pablo Molina in exploring important ethical issues when using information technology personally and professionally, including security, privacy, intellectual property, governance, inclusiveness, and diversity. Think about your own role and responsibility in the technology ecosystem of your organization.
IS&T Seminar Series - Envisioning YOUR Future

- Tuesday, April 10th 2018
- Frank Rabuck
- Rabuck Associates
The dynamics of a rapidly changing world make it a challenge to manage organizations and individual careers. Future success will be defined by those who “improvise, adapt, and overcome.” In this presentation Francis Rabuck will discuss some future technology roadmaps such as Quantum Computing, Augmented Reality, Robotics, AI, and IoT – and how organizations will need to adapt. He will also discuss tools to predict the future, why you need to use them, and some ideas on how future changes in the education system are critical to ensure worldwide progress.
IS&T Seminar Series - Technology Tracking in Higher Education

- Wednesday, November 15th 2017
- John Mulhern III
- University of Pennsylvania
Tracking technology in higher education is different from in many other sectors because universities are a set of vertical markets rather than a single one. In this presentation, John Mulhern III will use various visualization tools to show how technology adoption drives innovation and change. He will also discuss different ways of thinking about hardware and software lifecycles and how information technology organizations can use these constructs strategically.
IS&T Seminar Series - Trust in Wireless Networking

- Thursday, June 8th 2017
- Charles Rumford
- University of Pennsylvania
Wireless networking has become the primary method for connecting to networks whether it be at home, work, or the coffee shop down the street. But how do you know if you can trust the network you are connecting to? Come hear about different methods of how wireless networks are protected, different attack methods, and ways to help better protect yourself.
IS&T Seminar Series - It's an IT Evolution

- Thursday, May 25th 2017
- Kathryn Matuch
- Drexel University
Kathryn Matuch, Associate Vice President at Drexel University, will lead a discussion about reframing IT's relationship with the University to that of a Strategic Partner. Too often technology is relegated to the status of a utility - though 'keeping the lights on' is a very big part of what we do, to stay relevant and more importantly to grow and innovate, IT has to actively engage throughout the University to demonstrate that the skills and perspectives we have will improve business processes and strategies. We will discuss how this cultural shift is progressing at Drexel and what challenges and opportunities it introduces.
IS&T Seminar Series - Performance Insights

- Thursday, May 4th 2017
- Colleen Szymanik
- Comcast T&P
Understanding your network or service is essential to provide a solid user experience. Having the tools to prove your story or case through a variety of techniques can help with resources and planning. In this session, we will be identifying techniques to order and organize raw data into useful information. We will discuss measurements, determining key performance indicators, organization, and segregation of data as well as best practices with data analysis.
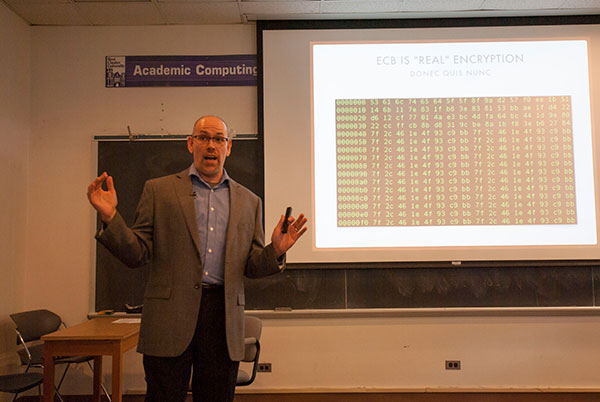
IS&T Seminar Series - The Edge of Chaos

- Wednesday, October 12th 2016
- Jon Moore
- Senior Fellow at Comcast Cable
In the technology industry, we are regularly faced with understanding complex systems -- which can only be understood holistically, and not as the sum of their parts -- with the limited capacity of our human brains. Moreover, our complex systems are developed and operated by people, which makes our overall sociotechnical systems complex adaptive systems with emergent behavior that wasn't contemplated when the system was first designed.
In this talk, we'll describe the nature of this problem and cover coping strategies drawn from control theory and other non-software contexts. We'll use this point of view to describe why Agile software development, DevOps, and microservices are business imperatives for avoiding falling over the "Edge of Chaos".
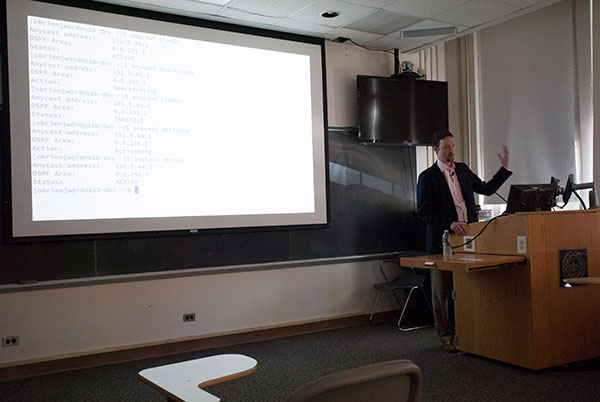
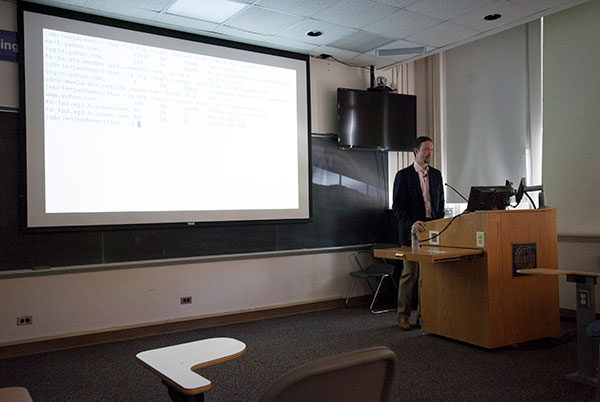
IS&T Seminar Series - In the Zone: Tales from the DNS

- Wednesday, October 5th 2016
- John O'Brien
- Network Architect at University of Pennsylvania
Between 2013 and 2015, the University of Pennsylvania implemented a significant update to the architecture of it's DNS service suite, built out a new DNS firewall service offering, and completed a major migration of campus clients. This discussion will cover significant technical accomplishments, including the deployment of anycast routing at the resolver tier, and reflections on the challenges and opportunities of operating DNS at institutional scale.
Penn's DNS infrastructure is absed on the BIND server, and is authoritative for about 1.1M resource records. The flagship zone, upenn.edu, has been DNSSEC signed since 2009. Query loads for the authoritative and recursive services peak at approximately 1.3kq/s and 6.9kq/s respectively.
IS&T Seminar Series - Infrastructure is Not Sexy...

- Wednesday, September 7th 2016
- Jorj Bauer
- Temple University
Why does it seem that good design principles often fall by the wayside? How do we identify and enact short-term solutions that help avoid long-term difficulties? Is this even possible? Have we done it before?
IS&T Seminar Series - Identity: What's All The Hubbub Bub?

- Monday, August 22nd 2016
- Michael Gettes
- Penn State University
For many years Identity Management has been at the fore of Higher Education issues. What's been happening? Where's it all going? And why do we care? Background, provocative thoughts, and discussion. Bring your own thoughts and voice.